A journey into IoT Forensics - Episode 4 - Analysis of an iRobot Roomba 690 (aka thanks VTO Labs for sharing!)
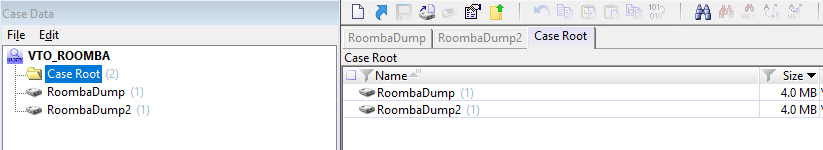
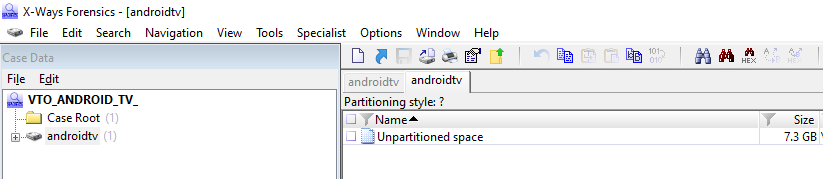
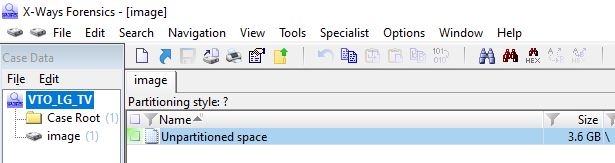
This the fourth blog post on the analysis of IoT devices images made available by VTO Labs . The first blog post was about the analysis of Samsung refrigerator , the second one was about the analysis of an LG Smart TV , the third one was about the analysis of an Ematic Android TV OS Box , and this one is about the analysis of an iRobot Roomba 690. [ START DISCLAIMER ] I only had one dataset, so the testing is limited and not to be considered strong and verified. The goal is to open a discussion and to provide a first glimpse into the analysis of these types of devices. [ END DISCLAIMER ] The iRobot Roomba 690 The fourth candidate for my research in the VTO Labs dataset was the image of an iRobot Roomba 690 , aWi-Fi Connected Robot Vacuum manufactured by iRobot Corporation. An old book (2006) on Hacking Roomba is available and the book website is still active . A forum on robot hacking is also available on Robot Reviews . I was not able to...