This the second blog post on the analysis of IoT devices images made available by
VTO Labs. The first blog post was about the
analysis of Samsung refrigerator and this one is about the analysis of an LG Television.
[START DISCLAIMER]
I only had one dataset, so the testing is limited and not to be considered strong and verified.
The goal is to open a discussion and to provide a first glimpse into the analysis of these types of devices.
[END DISCLAIMER]
The LG 55SK8000PUA Television
The second candidate for my research in the VTO Labs dataset was the image of an LG Television model 55SK8000PUA, a Smart TV produced by LG with the WebOS Operating System.
Various researches are available online about LG Smart TVs hacking and exploiting. A great resource is the SANE Lab website, managed by Prof. Seungjoo Kim. I suggest reading their works on LG and Samsung Smart TV:
On the Forensics side, I suggest reading:
Some of the mentioned papers and presentations already contain references to the analysis of WebOS devices, but most of them are based on previous versions of the OS.
Image verification and partitioning schema
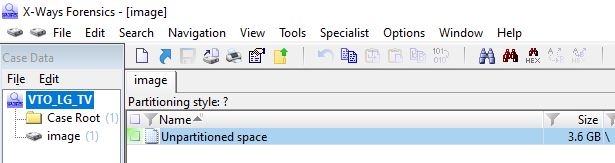
As in the case of the Samsung refrigerator, I tried loading the provided image (image.001) in X-Ways Forensics vers. 20.0. By simply loading the image, the tool was not able to find any partitioning schema.
I then used the "Scan for lost partitions" feature, and X-Ways found four EXT4 partitions.
MobileRevelator found four EXT4 partition: three of them (Partition 0, Partition 1 and Partition 2) were already found by X-Ways, while Partition 3 was found by MobileRevelator and not by X-Ways Forensics.
[UPDATE on 4th January 2021]
X-Ways version 20.1 SR-1, also based on this article, corrected the issue and can now find all the partitions.
Thanks Michael Yasumoto for the information and for your testing!
[END UPDATE]
TestDisk found four EXT4 partition, similarly to MobileRevelator
7-zip revealed a SquashFS at the beginning of the image.
The Squashfs has a Linux-style folder schema and seems to contain the WebOS files.I decided then to run "
binwalk" on the image: the tool found 6 SquashFS file systems.
Overall I found six SquashFS, extracted by binwalk and four EXT4 partitions, extracted by MobileRevelator and TestDisk: Partition 0 (/mnt/lg/uhdcp), Partition 1 (/var/db), Partition 2 (/mnt/lg/cmn_data) and Partition 3(/media).
SquashFS files
The six SquashFS files contain the stock LG WebOS. The "/etc/issue" file contains the operating system version. In the dataset it contains "webOS TV 3.5.0".
Partition 0 (/mnt/lg/uhdcp) and Partition 1 (/var/db)
Partition 0 (/mnt/lg/uhdcp) and Partition 1 (/var/db) don't seem containing useful data from a forensics perspective.

Partition 2 (/mnt/lg/cmn_data)
Partition 2 (/mnt/lg/cmn_data) seems containing the most interesting files from a forensics perspective.
The "/.iot/accountInfoFile" file contains a username, apparently related to the Amazon Echo service. In the provided dataset three values seem interesting: userID, userNo and aliasName.
The "/.iot/networkInfoFile" file contains the device name (in the provided dataset "[LG] webOS TV SK8000PUA")
The "/btsvc/mtk.conf" file contains:
- the TV Bluetooth name (in the provided dataset "[LG] webOS TV SK8000PUA")
- the TV Bluetooth MAC Address (in the provided dataset "00:51:ed:2b:db:27", manufactured by LG Innotek)
- the paired LG MR18 remote controller Bluetooth MAC Address (in the provided dataset "98:f5:a9:da:aa:f5")
The "/btsvc/mrcu1.info" file contains additional details about the remote controller, including the firmware version.
The "/btsvc/pairing_history" file contains information about remote controller pairing, including timestamps.
The "
/btsvc/bluedroid-mtk/rec/bluedroid/bt_config.conf" file contains additional information about paired devices.
The "
/channel_logo/major_logo_img" folder contains TV channels images an related JSON files.
The "/irdbmanager/setting/oss_setting_info_stb.txt" file contains information about the connected Set Top Box. In the provided dataset the Set Top Box is manufactured by "Direct TV" and connected on HDMI_1 port. The service name is "DirectTV(Denver)".
The "
/var/lib/connman/" file contains information about connected Wi-Fi

.
The "
/var/luna/data/downloadhistory.db" file contains information about installed applications. An embedded JSON file for each installation is available. It contains information about the specific app, including timestamps. In the specific dataset various apps are installed like Netflix, Amazon Prime Video, Vudu, ChannelPlus, Sling and YouTube.
Various Chrome-style Localstorage databases are stored in the profile. Among the others, the "lgappstv.com" contains last use date for each installed app.
The "/var/luna/preferences/" folder contains various TV settings and preferences.
The "/var/luna/preferences/localtime" file contains the local timezone. In the provided dataset "/usr/share/zoneinfo/America/Denver".
The "/var/luna/preferences/option" file contains various TV settings, including the ZIP code. In the provided dataset "80020", that corresponds to "Broomfield, Colorado" where VTO Labs is located.
The "/var/luna/preferences/locl" file contains the SHA-256 value of the System PIN. In the provided dataset the value is "9af15b336e6a9619928537df30b2e6a2376569fcf9d7e773eccede65606529a0" that corresponds to the PIN "0000".

The "/var/luna/preferences/systemprefs.db" file contains various system preferences, including the local timezone.
Some other interesting files in the "/var/luna/preferences/" folder are:
- time
- twinTV
- channel
- environmentCondition
- localeinfo
The "/var/spool/" folder contains various log files.
For example, the "analytics_log_NNN.tgz" files, contain information about app launch, and other user actions. More research is definitely needed on these logs, but they are for sure useful to build a usage timeline.
The "
/webbrowser/chrome/Default"
folder contains the internal web browser data. The WebOS Web Browser is based on Chromium, so the content of the folder can be easily parsed with
Hindsight.
In the provided dataset I found three Google searches ("calendar", "aol mail", "sprout"), a login on AOL.com with a specific email address and a login on Facebook.com.
Partition 3 (/media)
Partition 3 (/media) contains user data and third-party applications binary files, libraries and configuration.
The "cryptofs/apps/usr/palm" folder contains third-party application binary files, libraries and configuration.
The "
cryptofs/apps/var/lib/status" file contains third-party application details, including
installation date.
According to previous papers:
- "captureTV" folder should contain captured images
- "internal" folder should contain user files (wallpapers, downloads, ringtones)
- "myphoto" folder should contain user photos
In the provided dataset all of these folders are empty.
Conclusions
During the analysis I was able to find:
- Device hardware and software information
- Account information
- Network settings (Bluetooth and Wi-Fi)
- TV settings
- Timezone and ZIP code
- List of installed apps
- Browsing history
- Usage logs
- Media files
Again, more research is definitely needed in this field and I really hope to find soon new images to validate and improve these findings. If you have any additional image to share for research, you are very welcome!
I encourage you to provide me any kind of feedback and verify my findings. I'll update the blog post mentioning and thanking the reader.





































Comments
Post a Comment