A journey into IoT Forensics - Episode 5 - Analysis of the Apple HomePod and the Apple Home Kit Environment (aka thanks RN Team!)
This is the fifth blog post on the analysis of IoT devices. The first blog post was about the analysis of Samsung refrigerator, the second one was about the analysis of an LG Smart TV, the third one was about the analysis of an Ematic Android TV OS Box, and the fourth one was about the analysis of an iRobot Roomba 690. All the previous blog posts were based on images made available for research by VTO Labs.
This fifth post is about the acquisition and analysis of the Apple Homepod and the Apple HomeKit environment. This is based on a research developed by our RN team during 2020: in particular, it was the research topic of the thesis of our internship Francesca Maestri, who successfully obtained her computer science degree last year. Congrats and thanks for your great work Francesca!
The HomePod and the Home app
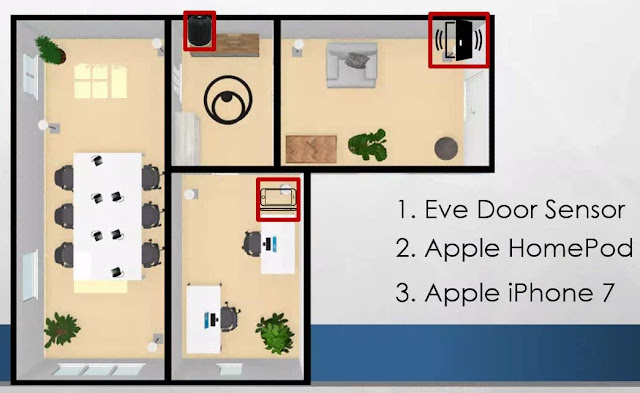
- An Apple HomePod, version 2018
- An Apple iPhone 7,
- A door sensor "Eve Door", compatible with Apple HomeKit
Data extraction
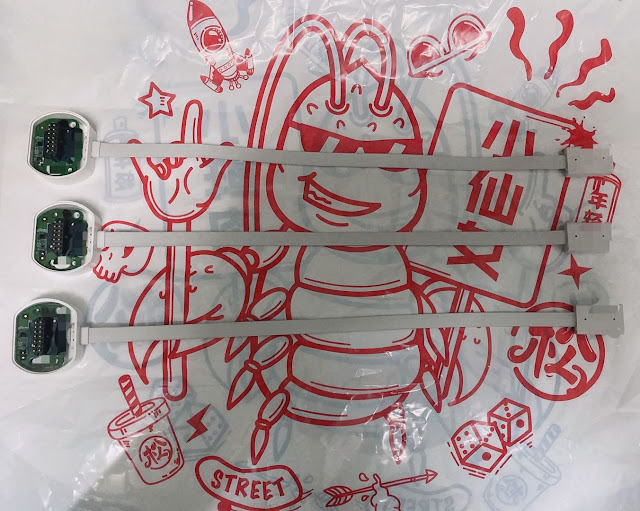
During our research, we were not able to find a viable solution to directly extract data from the Apple HomePod. The iFixt website published a teardown of the Apple HomePod, that revealed a 14-pin connector under the rubber base.
We recently found a "tweet", showing a possible adapter, but we were not able to find it on the market.
We decided then to analyze HomePod data in two ways:
- Generate and extract HomePod sysdiagnose logs
- Acquire and analyze the synced iPhone
Data analysis
Data analysis: synced iPhone
Device information and settings
- uuid: record identifier
- parent_uuid: parent uuid identifier
- type: a group which the specific record belongs to
- data: a BLOB object (a binary plist file)
By analyzing the
database, we noticed a hierarchy among the various elements, based on the uuid and parent_uuid columns. Here follows some of our findings:
- HMDHomeManagerModel is the main element in the hierarchy and the parent of HMDHomeModel
- HMDHomeModel is the parent of HMDRoomModel and HMDAppleMediaAccessoryModel
- HMDAppleMediaAccessoryModel is the parent of HMDAccessorySettingGroupModel
- Manufacturer
- Model
- Serial Number
- Firmware Version
- Custom Name
- WiFi
- en-US, is the language
- en-GB, is the accent
- f, is the genre
- The last value refers to the default combination ("en-US,en-US,f"): if the user changed it, the value is "n", otherwise is "d"
User interactions
SELECT
DATETIME(ZOBJECT.ZSTARTDATE+978307200,'UNIXEPOCH') AS "START",
DATETIME(ZOBJECT.ZENDDATE+978307200,'UNIXEPOCH') AS "END",
ZSTREAMNAME AS "STREAM NAME", ZVALUESTRING AS "VALUE
STRING", Z_DKNOWPLAYINGMETADATAKEY__TITLE AS "TITLE",
Z_DKNOWPLAYINGMETADATAKEY__ARTIST AS "ARTIST",
Z_DKNOWPLAYINGMETADATAKEY__ALBUM AS "ALBUM",
Z_DKNOWPLAYINGMETADATAKEY__DURATION AS "DURATION",
Z_DKNOWPLAYINGMETADATAKEY__GENRE AS "GENRE",
Z_DKNOWPLAYINGMETADATAKEY__MEDIATYPE AS "MEDIA TYPE",
Z_DKNOWPLAYINGMETADATAKEY__OUTPUTDEVICEIDS AS "OUTPUT DEVICE ID"
FROM
ZSTRUCTUREDMETADATA JOIN ZOBJECT
ON
ZOBJECT.ZSTRUCTUREDMETADATA = ZSTRUCTUREDMETADATA.Z_PK
ORDER BY ZOBJECT.ZSTARTDATE
you can obtain a list of played song.
By analyzing the binary plist file contained in the "Output Device ID" column you can obtain the device UUID.
The "/private/var/mobile/Library/com.apple.siri.inference/srdb.db" contains references to song played by using the Siri voice assistant. The table "entries" contains the song name (content_tokens column), the first time the song was played by using Siri (created_at column) and the last time the song was played by using Siri (modified_at column).Data analysis: Sysdiagnose
- The "/logs/Networking/preferences.plist" file that contains the HomePod Name set by the user
- The "/WiFi/com.apple.wifi.plist" file that contains information about Wi-Fi networks the device was connected to (SSID, BSSID, connections timestamps information about the network device (“WPS_PROB_RESP_IE”), and so on)
- The "/ioreg/IODeviceTree.txt" file that stores the manufacturer, the serial number, and the model name used by Apple to identify the HomePod (“AudioAccessory1,1”)
- The "logs/MobileActivation/mobileactivationd.log.*” files are the Mobile Activation logs. They can be used to obtain the operating system (iOS) version and its upgrades, along with the “Device Class” and “Product Type” assigned by Apple. These logs can be parsed with the Sysdiagnose Mobileactivationd Plist script
- The "logs/PowerLog” folder contains the HomePod PowerLog. By simply renaming the file as "CurrentPowerlog.PLSQL" you can easily run APOLLO against it.
Several modules could parse our database, and we obtained results about application info, device status, network usage, and so on.
- The "system_logs.logarchive" folder contains the HomePod syslog. Here you can find a lot of details about user actions, but this is typically restricted to the last hours of activities. For example you can find information about played radios and songs.
Data analysis: Eve Door Sensor
- “HMDAccessoryTransaction” group type, whose parent is “HMDHomeModel”. The embedded plist file contains door sensor manufacturer, model, serial number and room.
- “HMDServiceTransaction” group type, whose parent is “HMDAccessoryTransaction”. The embedded plist file contains the sensor name in the HomeKit environment
Conclusions
- We were not able to find a proper connector to directly interact with the Apple HomePod
- We were able to generate and extract the HomePod Sysdiagnose logs
- We extracted and analyzed the paired iPhone
- HomePod basic information (serial number, os version, name, and so on)
- HomePod settings
- HomePod geolocation
- Home organization in "Rooms"
- Connected HomeKit device
- User interactions (played songs)
- Door sensor information and usage logs
- HomePod basic information (serial number, os version, name, and so on)
- HomePod settings
- HomePod network connections
- HomePod PowerlLogs
- HomePod Syslog Archive




































Comments
Post a Comment